User provisioning with an Identity Provider (IdP)
Overview
Identity Providers (IdPs), such as Microsoft Entra ID or Okta, provide a directory of employees and can be used to manage employee app provisioning (for apps like Front). Front integrates with Identity Providers to enable automatic user provisioning, de-provisioning and group sync.
Supported Identity Providers
Identity Provider | User provisioning and de-provisioning User accounts are blocked in Front when an Identity Provider de-provisions them | Create new user with teammate Template | Sync group membership |
Microsoft Entra ID (previously Azure Active Directory) | ✅ | ✅ | ✅ |
✅ | ✅ | ✅ | |
✅ |
|
| |
OneLogin | ✅ | ✅ | ✅ |
Rippling | ✅ |
|
|
Gusto | ✅ |
|
|
Syncing groups from an Identity Provider
Identity Providers allow you to create user groups based on criteria such as department, job title or project. When you integrate an Identity Provider with Front, it is possible to sync those groups to a teammate group in Front.
When a group is pushed or assigned from an Identity Provider, a new teammate group will be created in Front. However, if a teammate group already exists in Front with the same name, the teammate group in Front will not be synced to the group in the Identity Provider.
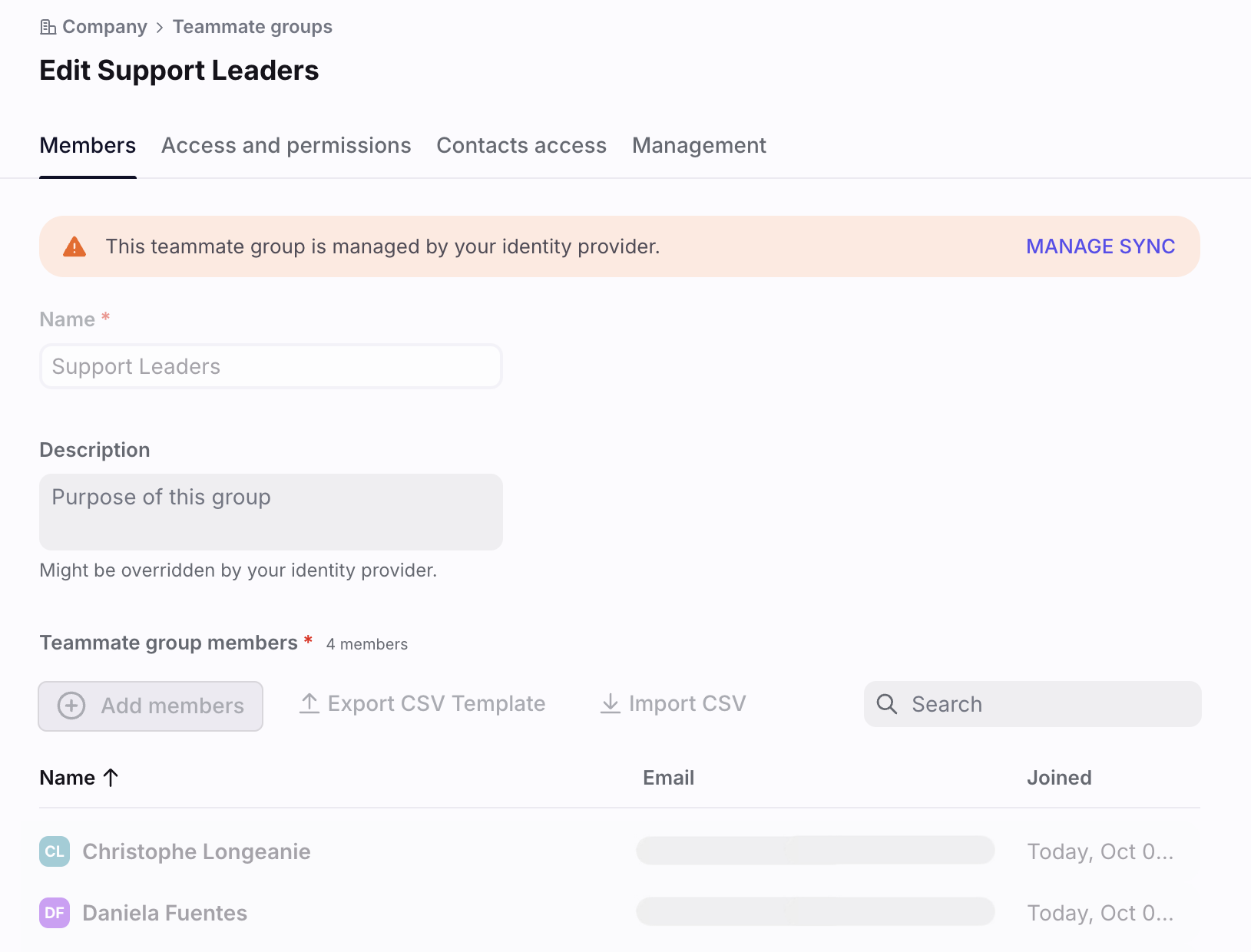
Identity Provider-managed groups in Front
Once a group is assigned to Front from an Identity Provider (IdP) like Okta, the teammate group in Front will be classified as IdP-managed. You can see if a teammate group is IdP managed by clicking on the group and checking for a banner at the top of the page.
Once a group is classified as IdP-managed, you cannot edit the group name and members inside Front. It is not possible to delete an IdP-managed group in Front; it must be deleted or unassigned from the Identity Provider.
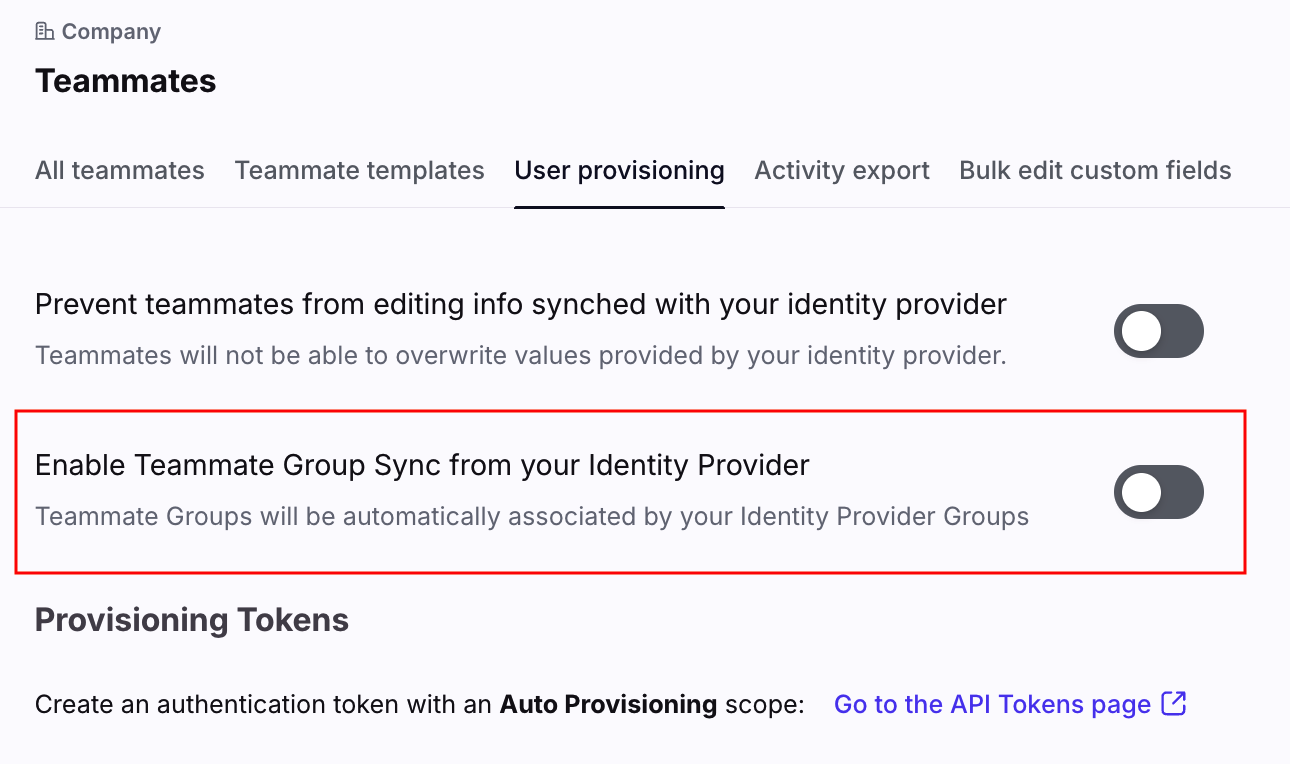
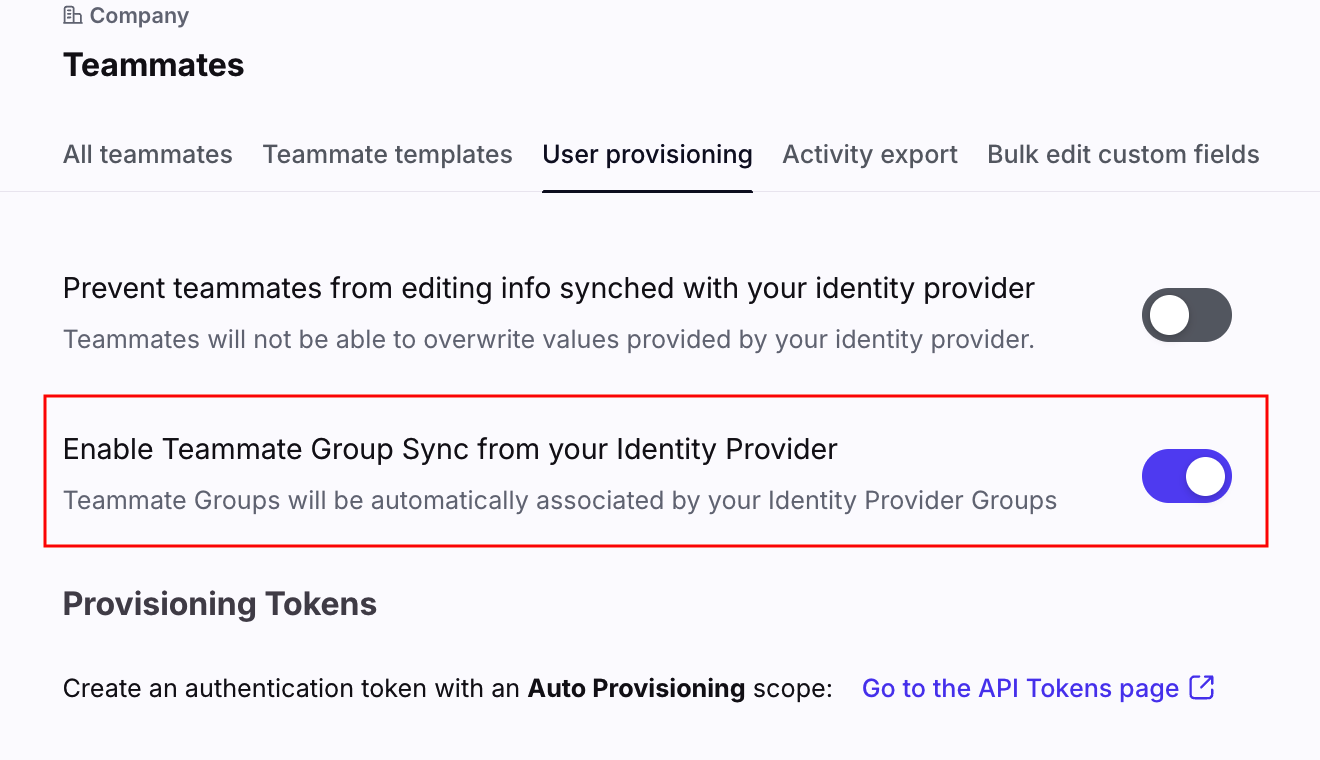
If you no longer wish to manage any groups from your Identity Provider, and would like to manage them inside Front instead, you can disable teammate group sync. To do this, navigate to your company settings, and select Teammates in the navigation sidebar, then click the User provisioning tab.
Integrating an Identity Provider with Front
Instructions to implement the integrations with an Identity Provider can be found in the table above or in the Identity Provider’s help center. For all Identity Providers, you will first need to configure a Front API token to pass to the Identity Provider.
Step 1
In Front, follow the steps on this article to create an API token.
Step 2
In the Feature access page, select Auto-provisioning. Click Create to finish creating the API token.
Step 3
If you want to push groups from your Identity Provider to teammate groups in Front, select Teammates in the navigation sidebar. Select the User provisioning tab, then toggle on the Enable Teammate Group Sync from your Identity Provider setting.
Step 4
Click on the token you created to copy it to your clipboard, and follow the Identity Provider’s instructions on where to save that token in the Identity Provider portal.
Integrating with other Identity Providers (SCIM API)
Front integrates with IdPs through a dedicated public API which follows the SCIM protocol. As we closely follow the protocol standards, in some cases, you may be able to integrate Front by creating a custom application in your IdP. For a custom application, you can generate a token as described above and access the SCIM API on the base URL:
https://scim.frontapp.com/v2Additional notes for developers building an integration with Front:
We follow the SCIM 2.0 protocol as documented here, supporting users and groups. PATCH requests are supported for both users and groups.
For full information on which fields we support, please refer to these endpoints:
https://scim.frontapp.com/v2/ServiceProviderConfighttps://scim.frontapp.com/v2/ResourceTypeshttps://scim.frontapp.com/v2/SchemasPricing
This feature is available on the latest Professional plan or above. Some legacy plans may also have access to this feature.